Critical Threat Intelligence & Advisory Summaries

Vulnerability Management: Operational Risk & Exposure-Based Prioritization
Executive Overview
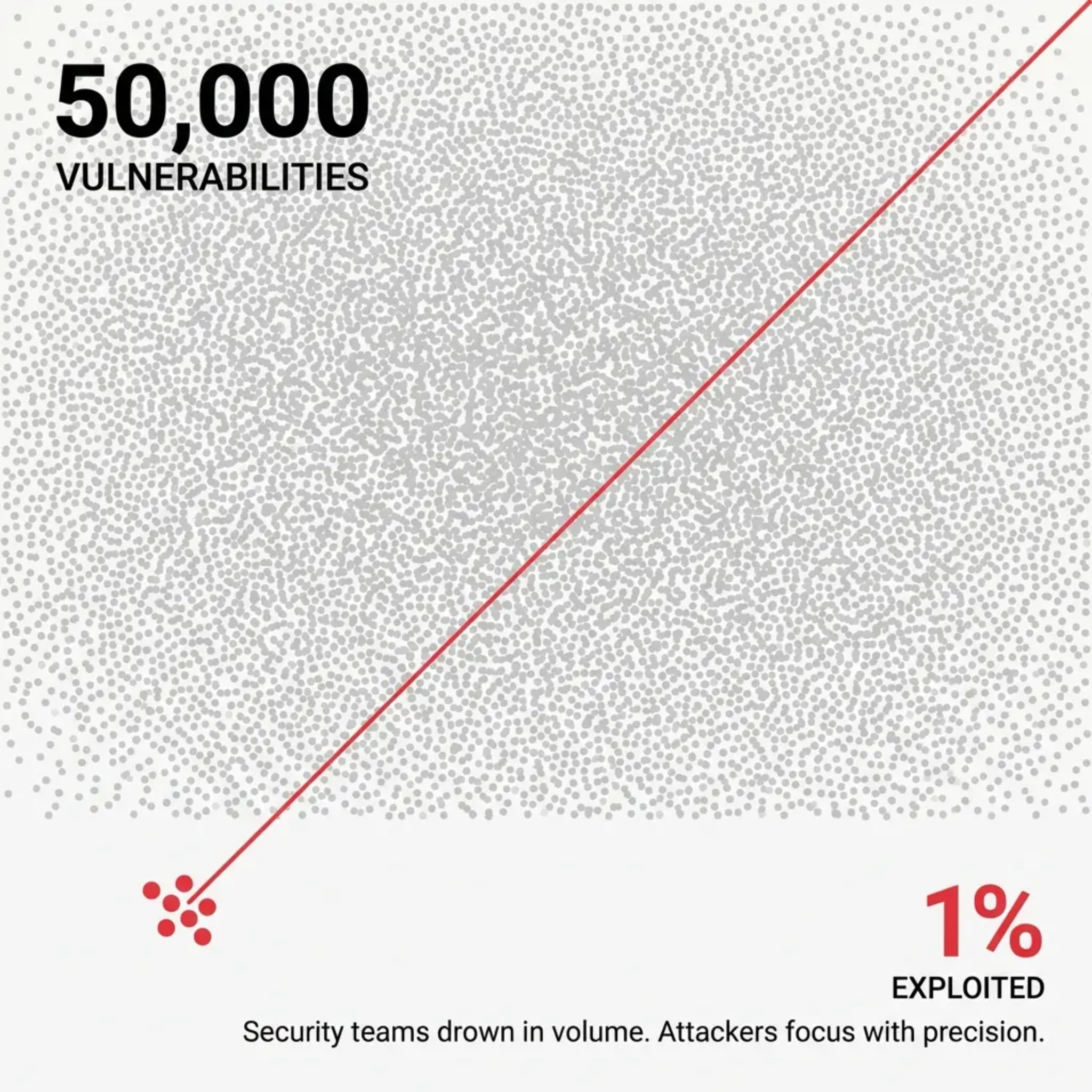
Organizations patch thousands of vulnerabilities annually while attackers exploit a tiny, predictable subset. Traditional severity-based frameworks, like CVSS, often fail to guide remediation efforts because attackers prioritize operational value, exposure, and exploit availability.
In 2025, barely 1% of disclosed vulnerabilities were actively exploited. Those exploited caused outsized damage before organizations could respond. EPSS and exploitation intelligence provide predictive, actionable guidance, moving teams from theoretical risk to operationally relevant prioritization.
The Exploitation Acceleration Problem
▪️28.96% of KEVs showed exploitation on or before disclosure day in 2025, up from 23.6% in 2024 (VulnCheck).
▪️Zero-day exploits increased 46% in H1 2025 alone (Cybernews).
▪️Exposure windows now collapse from days to hours; attackers industrialize reconnaissance, automate exploit chaining, and share tooling, compressing time-to-weaponization.
Mass Exploitation Campaigns
▪️MOVEit: Vendor software exploited to compromise hundreds of downstream organizations.
▪️CitrixBleed: NetScaler ADC and Gateway targeted for session token harvesting, MFA bypass, and persistent access.
▪️ProxyShell/ProxyNotShell: Microsoft Exchange servers exploited for RCE, web shell deployment, credential harvesting, and lateral movement.
Operational characteristics:
▪️Target internet-facing infrastructure with privileged network positions.
▪️Exploit systems lacking endpoint detection.
▪️Act before patching cycles complete.
▪️Enable ransomware deployment or espionage operations.
Internet-Facing Infrastructure as Primary Exploitation Surface
▪️48% of 2025 zero-days targeted enterprise technologies, predominantly networking and security appliances (Google Threat Intelligence).
▪️Edge infrastructure (firewalls, VPNs, proxies) offers maximum exposure and operational value.
▪️Exploitation provides privileged network positions, credential access, detection evasion, and persistent footholds.
China-nexus threat actors doubled zero-day activity from 2024, focusing on hard-to-monitor edge infrastructure.
Why Vulnerability Management Programs Fail
▪️CVSS prioritization inflates risk: 32.7% of vulnerabilities rated Critical or High, overwhelming remediation pipelines.
▪️CVSS does not predict exploitation; theoretical severity often misaligns with attacker behavior.
▪️Real-world exploitation disconnect: only 10.13% of known vulnerabilities had publicly available exploits; some high EPSS vulnerabilities scored only CVSS 5.5 (HivePro).
Operational failure points:
▪️Patch backlog overload
▪️Incomplete asset visibility
▪️Unmanaged edge infrastructure
▪️Slow remediation pipelines
Over 60% of KEVs are remediated after CISA deadlines, with critical vulnerabilities taking 4.5 months on average to patch (BitSight)
Integrating EPSS into Prioritization
The following table demonstrates how exploitation intelligence differentiates between "Critical" noise and "Critical" risk using real-world data from the current threat landscape.
| Vulnerability |
CVSS |
EPSS Score |
KEV Confirmed |
Exploit Available |
Internet Exposure |
Asset Criticality |
Remediation Priority |
| CVE-2025-53770 (SharePoint RCE) | 9.8 | 0.96 | ✅ | ✅ | High | High | CRITICAL |
| CVE-2025-0108 (Palo Alto Auth) | 9.3 | 0.89 | ✅ | ✅ | High | High | CRITICAL |
| CVE-2025-11953 (React Native) | 9.8 | 0.15 | ✅ | ✅ | Medium | High | HIGH |
| CVE-2025-55752 (Apache Tomcat) | 7.5 | 0.003 | ❌ | ✅ | Medium | Medium | MEDIUM |
| CVE-2026-0960 (Wireshark DoS) | 5.5 | 0.01 | ❌ | ❌ | Low | Low | LOW |
Why Internet Exposure is the Multiplier
The inclusion of the Exposure column reflects the "Reachability" factor now central to CISA’s 2026 Internet Exposure Reduction Guidance:
▪️The "Edge" Crisis: Both CVE-2025-53770 and CVE-2025-0108 targeted edge infrastructure. Their "High" exposure meant that automated scanners (Shodan, Censys) could identify targets within minutes of the exploit being weaponized. This is why their Remediation Priority is CRITICAL—the time-to-exploit is measured in hours, not days.
▪️The Internal Shield: In contrast, CVE-2026-0960 (Wireshark) has a "Low" exposure because it requires a local attacker to capture a specifically malformed packet. Even if the CVSS were higher, its lack of internet reachability keeps it at a LOW priority.
▪️The SSVC Logic: CISA and FIRST now advocate for a "Decision Tree" approach. If Exposure = High AND EPSS > 0.10, the asset moves into the "Act" category immediately.
Operational Impact
By reporting on Internet Exposure, you are aligning with the Continuous Threat Exposure Management (CTEM) trend. Organizations that prioritize based on exposure are reported to be 3x less likely to suffer a breach in 2026 because they close the entry points attackers use for initial access.
Asset Criticality acts as the final decision-maker. As noted in the HackerStorm tip earlier, a high-probability exploit (EPSS 0.90) on a "Low Criticality" isolated test lab ranks lower than a medium-probability exploit (EPSS 0.40) on a primary production Database.
SOC Checklist: Exploitation-Led Prioritization (2026)
Use this workflow to triage the daily influx of CVEs by moving from generic global probability to organization-specific risk.
Phase 1: High-Signal Filtering (The 1% rule)
[ ] Identify KEV Status: Is the CVE in the CISA KEV Catalog?
Action: If YES, bypass standard SLA. Initiate Emergency Patching (Target: <48 hours).
[ ] Analyze Global EPSS Probability: Is the EPSS Score 0.10 (10%)?
Action: Any vulnerability with a >10% probability of exploit in 30 days is a top-tier priority.
Phase 2: Contextual Rating Enhancement (HackerStorm Engine)
Rather than relying on generic scores, use HackerStorm’s contextual engine to adjust the EPSS rating based on reported breach data and APT activity specific to your profile:
[ ] Organizational Profile Adjustment: Refine the score based on Business Sector, Location, and Organization Size.
Insight: Threat actors often target specific industries (e.g., Financial Services vs. Manufacturing) with specialized tooling.
[ ] Environmental Visibility Weighting: Is the asset located in a Partner, Internet, Corporate, or Highly Isolated environment?
Action: Escalate internet-facing and partner-connected assets immediately; deprioritize highly isolated environments even if the global EPSS is high.
[ ] Security Maturity & User Type: Factor in internal controls and the primary user base (e.g., Customer type vs. Staff) to calculate the realistic likelihood of a successful breach.
Phase 3: Operational Validation
[ ] Threat Actor Alignment: Does HackerStorm indicate current APT or known threat actor activity targeting this specific vulnerability within your sector?
[ ] Detection & Mitigation: Do we have SIGMA or YARA coverage? If patching is delayed, is a Virtual Patch (WAF/IPS) viable for the specific environment type identified?
TIP:
HackerStorm.com provides contextual EPSS scoring, which weights vulnerability exploitation probability against your organization’s asset profile, exposure, and sector-specific threat data. This transforms generic EPSS into organization-specific actionable guidance.
KEV Catalog and Exploitation Intelligence
▪️ 884 KEVs identified in 2025 with 118 unique disclosure sources (VulnCheck).
▪️ Fragmented intelligence requires aggregation across vendor advisories, threat intelligence reports, honeypot observations, and incident response disclosures.
▪️ KEV vulnerabilities are remediated 3.5x faster, proving exploitation intelligence accelerates organizational action.
Operational Threat Intelligence for Vulnerability Prioritization
Security teams should integrate exploitation intelligence to prioritize based on:
1️⃣ Exploitation evidence – active attacks observed in the wild
2️⃣ Threat actor tradecraft – vulnerability targeting patterns
3️⃣ Internet exposure – externally accessible assets
4️⃣ Asset criticality – business impact
5️⃣ Exploit availability – proof-of-concept or weaponized code
This approach shifts vulnerability management from compliance-driven to risk-based, intelligence-driven remediation.
Key sources: CISA KEV updates, vendor advisories, threat reports, research disclosures, honeypot observations, incident response feeds.
Strategic Recommendations
SOC Teams:
▪️Detection engineering for edge and internet-facing infrastructure
▪️KEV integration into alert workflows
▪️Aggregation of exploitation intelligence for detection and patching
Vulnerability Management Teams:
▪️Exploitation-driven prioritization
▪️Exposure-based risk assessment
▪️Accelerated KEV remediation workflows
Security Architecture Teams:
▪️Comprehensive visibility for internet-facing and edge assets
▪️Network segmentation and access controls
▪️Edge infrastructure detection via NTA and behavioral monitoring
Hackerstorm.com Forward-Looking Assessment
1️⃣ Exploitation timelines will continue to compress.
2️⃣ Mass exploitation campaigns will expand beyond ransomware into espionage and supply chain compromise.
3️⃣ Edge infrastructure remains a top target due to privileged access and monitoring gaps.
4️⃣ Organizations relying solely on CVSS will face growing breach risk; exploitation intelligence becomes the differentiator.
Strategic Context & Further Reading
🔗 Why Most Patch Programs Fail: CVSS Overload, KEV Lag, and Exposure Blind Spots Why read this: Most vulnerability programs fail not due to lack of effort, but flawed prioritization logic. This article breaks down how CVSS inflation, delayed KEV response, and lack of exposure context create systemic blind spots and what to change to align patching with real-world exploitation risk.
🔗 Operational Threat Intelligence: Practical Guide for Security Teams Why read this: Prioritization requires context. This guide explains how to integrate threat intelligence into security operations helping teams move from reactive patching to intelligence-driven decision making.
🔗 FIRST 2026 Forecast: Record-Breaking 59,000 CVEs Signal "Strategic Shift" for Security Teams Why read this: Vulnerability volume is accelerating beyond human-scale prioritization. This analysis explains why record CVE growth forces a shift toward EPSS, KEV, and exposure-based models and how security teams must adapt to avoid being overwhelmed by noise.
🔗 MOVEit Mass Exploitation (OFA): KEV Prioritization and Internet-Facing Asset Visibility Failure Why read this: This analysis shows how a widely exploited vulnerability escalated into a global breach despite clear signals, KEV prioritization, and available patches—highlighting where vulnerability management and asset visibility break down under real-world attack conditions.
🔗 CVSS vs EPSS: How to Prioritise Vulnerabilities by Real Exploitation Risk Why read this: CVSS measures theoretical severity, but EPSS predicts real-world exploitation probability. Learn why modern vulnerability management must combine both to prioritise the risks attackers actually target.
|
About This Report
Reading Time: Approximately 15 minutes
This Threat Intelligence Brief is based on publicly disclosed corporate incident reports, U.S. law enforcement advisories, federal court records, and threat intelligence research from multiple cybersecurity organizations.
Information reflects the operational threat landscape as of February 2026.
Author Information
Timur Mehmet | Founder & Lead Editor
Timur is a veteran Information Security professional with a career spanning over three decades. Since the 1990s, he has led security initiatives across high-stakes sectors, including Finance, Telecommunications, Media, and Energy. Professional qualifications over the years have included CISSP, ISO27000 Auditor, ITIL and technologies such as Networking, Operating Systems, PKI, Firewalls. For more information including independent citations and credentials, visit our About page.
Contact:
Editorial Standards
This article adheres to Hackerstorm.com's commitment to accuracy, independence, and transparency:
- Fact-Checking: All statistics and claims are verified against primary sources and authoritative reports
- Source Transparency: Original research sources and citations are provided in the References section below
- No Conflicts of Interest: This analysis is independent and not sponsored by any vendor or organization
- Corrections Policy: We correct errors promptly and transparently. Report inaccuracies to
This email address is being protected from spambots. You need JavaScript enabled to view it.
Editorial Policy: Ethics, Non-Bias, Fact Checking and Corrections
Learn More: About Hackerstorm.com | FAQs
Sources
-
VulnCheck State of Exploitation 2026
-
VulnCheck 2026 Exploit Intelligence Report
-
BitSight KEV Remediation Research
-
CISA KEV Catalog Impact Analysis
-
Google Threat Intelligence 2025 Zero-Day Review
-
Cybernews Zero-Day Exploit Analysis
-
Security Boulevard Mass Exploitation Economics
-
HivePro CVSS Prioritization Analysis
-
HackerStorm.com Contextual EPSS Analysis
