Critical Threat Intelligence & Advisory Summaries
JLR Breach Analysis (OFA) - Third-Party Identity Exposure and KEV Prioritization Gaps
Operational Failure Analysis: OFA-2026-02-JLR:
1. Breach Snapshot
Target Organization: Jaguar Land Rover (JLR)
Operational Impact: Multi-week disruption to global manufacturing operations during 2025
Primary Access Vector (reported): Stolen third-party credentials combined with exploitation of SAP NetWeaver vulnerabilities
Confirmed Themes from public reporting:
• Third-party account compromise
• Data exfiltration
• Production shutdown across multiple facilities
• Earlier security incident earlier in 2025 preceding the major disruption
Note: This report is part of the Hackerstorm Operational Failure Analysis (OFA) series, a structured framework for analyzing operational failures in cybersecurity breaches and providing signal-driven insights for security teams.
Operational Relevance
This incident illustrates breakdowns across multiple control layers:
• Third-party identity lifecycle management
• Vulnerability prioritization for actively exploited enterprise software
• Detection and response following an initial breach event
2. Timeline of Signals (Defender Perspective)
Based on public reporting and vendor/security advisories.
| Approx. Date | Event | Signal Available to Defenders |
|---|---|---|
| Early 2025 | SAP NetWeaver security advisories issued | Patch availability for exposed enterprise systems |
| 2025 (prior to major incident) | CISA warnings / industry alerts on active exploitation (where applicable) | Known-exploited risk requiring accelerated remediation |
| March 2025 | Initial breach and data exposure reported | Confirmed targeting; trigger for credential rotation and third-party audit |
| Weeks before major disruption | Reported social engineering activity (vishing) targeting staff | Elevated identity threat activity |
| September 2025 | Major operational disruption and production shutdown | Containment and resilience failure |
| Late 2025–Early 2026 | Gradual operational recovery | Extended recovery timeline indicates deep operational impact |
Key insight:
This was not a zero-day scenario. Multiple defensive signals existed across the year.
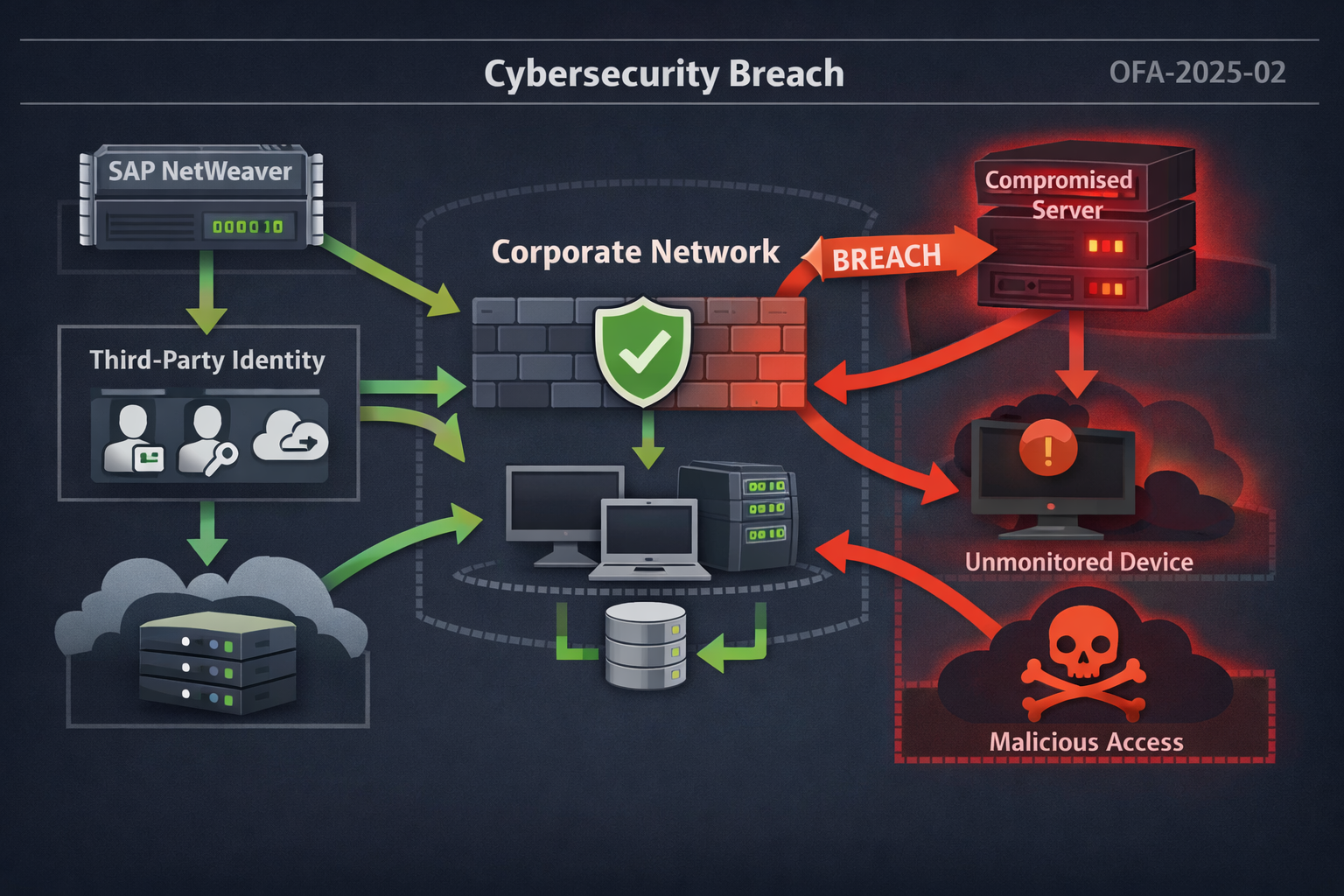
3. Exploit Chain (Reconstructed from Public Reporting)
While full forensic details are not publicly confirmed, reporting suggests the following attack path:
Initial Access
• Credentials harvested via infostealer malware or social engineering
• Access associated with a third-party user account connected to internal systems (including Jira/VPN)
Persistence
• Long-lived external credentials remained valid
• Limited lifecycle enforcement for third-party identities
Privilege & System Access
• Attackers leveraged enterprise application access
• Security researchers have linked the activity to exploitation of SAP NetWeaver vulnerabilities (attribution varies by source)
Lateral Movement
• Movement within corporate IT environment
• Potential pivot toward operational or production systems
Impact
• Large-scale data exfiltration (hundreds of GB reported)
• Global production shutdown as containment measure
4. Where the Control System Broke
Discovery Failure: External Identities as “Invisible Assets”
Public reporting indicates attackers used a third-party account.
Common failure patterns consistent with this scenario:
• External accounts not included in asset inventory
• No automated expiration for contractor access
• Limited monitoring of long-dormant accounts
• Third-party identities treated outside VM / risk workflows
Operational takeaway:
Identity is an asset class. If external accounts are not continuously discovered and validated, they become persistent access channels.
Identity Governance Failure
Indicators from reporting suggest:
• Credentials harvested years earlier may still have been valid
• Inconsistent enforcement of MFA across external access points
• No mandatory rotation following earlier breach activity
Control gap:
• Credential lifecycle and breach-response rotation procedures.
Operational Improvement: The "Kill-Switch" Protocol To address the "credential time bomb" (where 2021 credentials remained valid in 2025), operations should shift to Just-In-Time (JIT) Access:
• Just-In-Time (JIT) Provisioning: Contractor and third-party accounts should be "Disabled by Default." Access is only provisioned for a specific change window and automatically deactivated upon ticket closure.
• Automated Session Revocation: Following the March 2025 HELLCAT incident, a global "Revoke All" command should have been issued. Operations must have the capability to terminate all active OAuth tokens and forced re-authentication via phishing-resistant MFA (FIDO2) across the entire identity provider (IdP).
Prioritization Failure: Known Enterprise Software Risk
Security researchers and industry reporting have associated the incident with SAP NetWeaver vulnerabilities.
Where applicable, these issues were:
• Publicly disclosed
• Enterprise-critical
• Subject to security advisories and active exploitation warnings
Common failure conditions:
• Standard patch SLAs applied to high-risk enterprise platforms
• CVSS-only prioritization
• Lack of acceleration when vulnerabilities appear in CISA KEV or show exploitation activity
Operational takeaway:
Enterprise middleware (SAP, identity platforms, remote access systems) requires exploitation-driven prioritization, not standard patch cycles.
Technical Spotlight: The SAP NetWeaver "Open Door" (CVE-2025-31324)
To understand why standard patch cycles failed JLR, we must look at the specific vulnerability exploited: CVE-2025-31324.
• The Vulnerability: A missing authorization check in the SAP NetWeaver Visual Composer Metadata Uploader.
• The "God Mode" Exploit: It allowed unauthenticated attackers to send a simple HTTP request to the /developmentserver/metadatauploader endpoint and upload malicious JSP web shells.
• The Timeline Gap: * April 2025: SAP released an out-of-band "Emergency" patch.
- May 2025: Security vendors (Unit 42, Red Canary) reported active exploitation in the wild.
- September 2025: JLR production halted due to an exploit chain utilizing this exact flaw.
• The Lesson: Standard 30-day "Patch Tuesdays" are fatal for internet-exposed ERP systems. If a vulnerability hits CVSS 10.0 and appears on the CISA KEV list, remediation must happen in <48 hours, regardless of the maintenance window.
Segmentation Failure
JLR operates tightly integrated IT and production environments.
The operational shutdown suggests:
• Limited containment boundaries between corporate IT and manufacturing systems
• Inability to isolate compromised segments quickly
• High operational dependency on shared infrastructure
Operational Improvement: Purdue Model Enforcement The global production halt proves that the IT and OT (Operational Technology) layers were too interdependent. Resilience requires a Level 3.5 Industrial DMZ (IDMZ):
• No Direct Routing: Eliminate all direct IP routing between corporate applications (like SAP) and the factory floor. All data must terminate in a secured DMZ.
• Protocol Deep Packet Inspection (DPI): Firewalls must be configured to inspect industrial traffic (OPC-UA, Modbus). This ensures that even if an IT account is compromised, the attacker cannot send "Stop" or "Reprogram" commands to manufacturing PLC (Programmable Logic Controllers) without passing through a secondary, hardened "Jump Host."
5. Exploitation Intelligence Context
This incident reflects several patterns seen across enterprise breaches:
Identity-First Intrusion
• Initial access via stolen credentials
• Social engineering and infostealer ecosystems as primary access brokers
Enterprise Platform Targeting
• SAP, identity systems, and collaboration platforms remain high-value targets
• Exploitation often follows public disclosure rather than zero-day discovery
Signal-to-Impact Window
• Months between initial breach activity and operational disruption
• Opportunity window for:
- Credential reset
- Third-party audit
- Accelerated patching
- Threat hunting
Prioritization Model Implications
Operational intelligence sources (EPSS, KEV, active exploitation reporting) should override routine CVSS-based workflows when exploitation likelihood increases.
6. What Would Have Prevented or Contained This
Immediate Controls (48-Hour Actions)
Third-Party Identity Controls
• Inventory all external accounts
• Enforce MFA without exception
• Apply automatic expiration (≤90 days)
• Require credential rotation after any security incident
KEV / Exploitation Monitoring
• Automatically map assets to CISA KEV
• Apply accelerated remediation SLA (e.g., ≤14 days)
Containment Readiness
• Verify IT–OT segmentation
• Restrict administrative cross-network access via jump hosts
• Implement egress monitoring on sensitive data repositories
Structural Improvements (90-Day Changes)
Move to Exploitation-Driven Prioritization
• Integrate EPSS scoring
• Prioritize:
- KEV inclusion
- EPSS thresholds
- Public PoC availability
Event-Driven Asset Discovery
Monitor for:
• New external identities
• Dormant account activation
• New network services
• Cloud or SaaS integrations
Identity as an Asset Class
• Include identities in vulnerability/risk inventory
• Apply lifecycle governance equivalent to servers and applications
7. Sector Implications: Manufacturing
Manufacturing environments face elevated risk due to:
• IT/OT convergence
• Legacy operational systems
• High availability requirements
• Complex supplier and contractor access
Extended production disruption demonstrates that identity compromise in IT environments can become operational downtime.
8. Operator Checklist
If you run a security program, validate the following:
Identity
Are all third-party accounts inventoried?
Do external accounts expire automatically?
Is phishing-resistant MFA enforced?
Prioritization
Are KEV vulnerabilities auto-escalated?
Is EPSS used to adjust patch priority?
Discovery
Do you detect dormant account reactivation?
Are new external identities monitored?
Containment
Can IT and OT environments be isolated quickly?
Is egress monitoring enabled for sensitive systems?
Final Assessment
The JLR incident was not defined by advanced malware or zero-day exploitation. Public reporting indicates a combination of:
• Third-party identity exposure
• Known enterprise software risk
• Missed defensive signals over several months
For security teams, the primary lesson is operational:
Most large-scale disruptions now begin with identity exposure and escalate through known, detectable risk — not novel exploitation.
Organizations that treat external identities, enterprise platforms, and KEV exposure as routine risk are likely to face the same failure pattern.
Related Articles
🔗 Operational Threat Intelligence: Practical Guide for Security Teams
🔗 MOVEit Mass Exploitation (OFA): KEV Prioritization and Internet-Facing Asset Visibility Failure
About This Report
Reading Time: Approximately 15 minutes
This Threat Intelligence Brief is based on publicly disclosed corporate incident reports, U.S. law enforcement advisories, federal court records, and threat intelligence research from multiple cybersecurity organizations.
Information reflects the operational threat landscape as of February 2026.
Author Information
Timur Mehmet | Founder & Lead Editor
Timur is a veteran Information Security professional with a career spanning over three decades. Since the 1990s, he has led security initiatives across high-stakes sectors, including Finance, Telecommunications, Media, and Energy. Professional qualifications over the years have included CISSP, ISO27000 Auditor, ITIL and technologies such as Networking, Operating Systems, PKI, Firewalls. For more information including independent citations and credentials, visit our About page.
Contact:
Editorial Standards
This article adheres to Hackerstorm.com's commitment to accuracy, independence, and transparency:
- Fact-Checking: All statistics and claims are verified against primary sources and authoritative reports
- Source Transparency: Original research sources and citations are provided in the References section below
- No Conflicts of Interest: This analysis is independent and not sponsored by any vendor or organization
- Corrections Policy: We correct errors promptly and transparently. Report inaccuracies to
This email address is being protected from spambots. You need JavaScript enabled to view it.
Editorial Policy: Ethics, Non-Bias, Fact Checking and Corrections
Learn More: About Hackerstorm.com | FAQs
